Blog
Educate & Motivate
Discover more about managed services, cyber security, cloud solutions and much more.
The blog section of our website contains a wide array of interesting and useful posts, covering the full spectrum of business IT topics. We will share important advice on how to protect your business from common threats, offer tips on how to plan for disasters, and explain the true value of some of the services we provide - all with a view to helping you to become more informed and better equipped to tackle modern business challenges.
If you have a more specific query don’t hesitate to get in touch.
Fifosys Blog and Resources
XDR vs MDR: What’s the Difference, and Which One Does Your Business Need?
Confused by XDR vs MDR? Here’s what UK SMEs and mid-market organisations need to know about modern threat detection, why endpoint security alone is no longer enough, and how broader visibility plus managed response can help reduce blind spots across email, cloud, identity, endpoint, and network environments.
The CISA GitHub Leak Is a Mess. But It’s Also Very Familiar
A major credential leak linked to the US cybersecurity agency CISA has exposed a problem most businesses are far more vulnerable to than they realise. From forgotten API keys to overprivileged supplier access, exposed credentials have become a normal part of modern IT environments. Here’s what UK SMEs and mid-market organisations should actually be paying attention to.
When Supply Chain Attacks Become a Competition: What UK Businesses Need to Pay Attention to
A new threat advisory issued in May 2026 warns of increased risk around software supply chain compromise, including underground activity that appears to reward scale and downstream impact. For UK SMEs and mid-market organisations, the takeaway is not panic. It is a reminder that modern cyber risk does not always start inside your business.
Unpacking Microsoft’s MFA Push: An Operations Check for Your Business
Microsoft’s MFA enforcement is not just another login tweak. For UK SMEs and mid-market organisations, it is a useful prompt to review admin access, legacy accounts, automations, and whether Microsoft 365 is being actively managed or simply inherited.
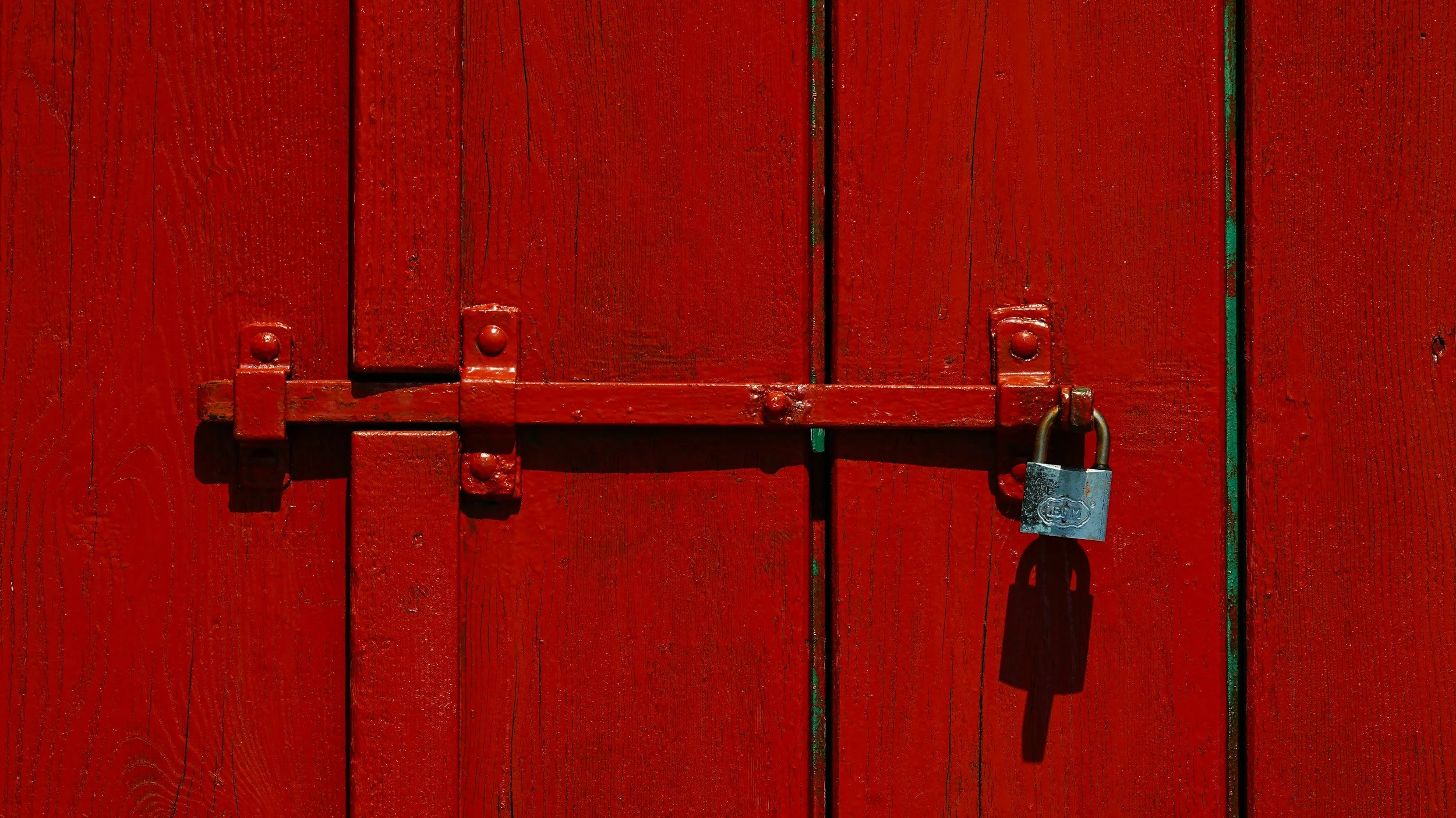
Locking the Door: A Simple Cyber Hygiene Checklist for 2026
Cyber security doesn’t always come down to complex tools or advanced threats. More often, it’s the basics that make the biggest difference.
Following the UK government’s “lock the door” campaign, we’ve pulled together a simple cyber hygiene checklist to help organisations sense-check their current approach, from patching and access control to visibility and response.
The Five Assumptions That Lead to Breaches
Cyber incidents aren’t always the result of sophisticated attacks. More often, they stem from everyday assumptions about how systems work, where responsibility sits, and who is actually at risk.
With around half of UK SMEs experiencing a breach or attack in the past year, it’s clear that those assumptions don’t always hold up. In this blog, we explore five common beliefs that continue to catch organisations out, and why they’re worth challenging.
Don’t Be Fooled: 5 Phishing Tactics to Watch Out for (And How to Spot Them)
April Fools’ Day is built on harmless deception, but phishing attacks are anything but. While prank emails might raise a smile, malicious ones are designed to catch you off guard and exploit trust, urgency or familiarity.
In this blog, we break down five common phishing tactics still catching people out in 2026, and what to look for before you click.
Cyber Essentials vs Cyber Essentials Plus: What’s the Real Difference?
Cyber Essentials has become a baseline requirement for many UK organisations, whether for supply chains or government contracts. But as more businesses look beyond the badge, a key question keeps coming up: is Cyber Essentials enough, or does Cyber Essentials Plus offer something more meaningful?
In this blog, we break down the real difference between self-assessment and independent validation, and why that distinction matters when it comes to understanding your actual security posture.
What the Companies House Incident Reveals About Cyber Risk
Companies House is one of those systems most people assume simply works. It sits quietly in the background of the UK business environment, holding records for millions of companies and underpinning how organisations verify each other every day.
But recent reports of a vulnerability in the WebFiling system have raised serious questions about how secure that infrastructure really is. Beyond the technical issue itself, the incident highlights something broader: many of the systems businesses rely on sit outside their direct control.
When platforms like this experience problems, the consequences can ripple far beyond the organisation running them.
Locking the Door: Why Basic Cyber Hygiene Still Matters in 2026
The UK government has launched a campaign urging businesses to “lock the door” on cyber criminals, highlighting a simple truth: many attacks succeed because basic protections are missing. From weak passwords to unpatched systems, small gaps can create big risks. Here’s why cyber hygiene still matters in 2026 and why the fundamentals remain your strongest defence.
What Is DMARC? Why Domain Protection Matters in 2026
Email remains one of the most trusted channels in business, yet it is also one of the easiest to abuse. If your domain is not properly protected, it can be spoofed without your knowledge, putting your brand and clients at risk. In this piece, we break down what DMARC actually does, why so many organisations still misconfigure it, and why domain protection should be treated as a baseline control in 2026.
What the ChatGPT Caricature Craze Really Reveals About Privacy and AI Risk
ChatGPT caricatures are everywhere right now. They’re fun, personalised, and feel low risk. But beneath the surface sits a more uncomfortable reality about data permanence, profiling and workplace exposure. This blog breaks down what’s actually at stake when we feed AI more detail than we realise.
Fifosys Becomes a CyberSmart Advanced Partner: What That Means for Our Customers
Cyber Essentials and Cyber Essentials Plus remain a critical foundation for managing cyber risk and meeting UK compliance requirements. Fifosys has been promoted to CyberSmart Advanced Partner status, reflecting the scale and quality of how we already support customers through certification and beyond.
Instagram Security Incident: Password Reset Emails, Data Exposure, and What It Means for Cyber Risk
Millions of Instagram users received unsolicited password reset emails over the weekend. We examine what happened, the data exposure risks, and the security lessons for organisations.
2025 in Review: The Cyber Incidents That Redefined Risk and Resilience
2025 was a defining year for cyber security. From major outages to supply-chain attacks, organisations were forced to confront systemic risk and the limits of assumed resilience. This review examines the cyber incidents that mattered and the lessons they hold for the year ahead.
The Rainbow Six Siege Breach and the Hidden Cost of Holiday Cyber Risk
The Christmas period is meant to be quiet, yet the Rainbow Six Siege breach shows how cyber incidents thrive when attention drops. As servers were taken offline and data integrity collapsed, the real story goes beyond gaming disruption, revealing the risks that always-on services face when attackers strike during holiday downtime.
Every Minute Counts: The Case for Proactive Monitoring
Cyberattacks are rising fast, with one hacking incident now happening every minute. Across the Fifosys client base, we’re seeing record volumes of suspicious logins, phishing emails, and attempted breaches.
In a reactive setup, remediation can take hours long enough for attackers to forward data, alter rules, or move laterally through systems.
This blog explores how proactive monitoring powered by Barracuda Managed XDR is closing that gap, reducing response times from hours to minutes, and giving organisations constant visibility across their cloud environments.
The True Cost of Not Investing in Security
When thieves broke into the Louvre Museum, the biggest shock wasn’t what they stole - it was how easily they did it. Yet, a password allegedly set to “Louvre” is what’s really exposed one of the world’s most secure institutions. The incident is a reminder that under-investment in cyber security doesn’t just risk data loss; it threatens trust, reputation and millions in avoidable cost.
Why Preparation Has Replaced Prevention
Another year is closing out, and once again, cyber security has dominated the agenda. From AI-powered attacks to boardroom accountability, 2025 has challenged every layer of digital resilience. As new threats rise and regulations tighten, UK organisations are learning that prevention alone isn’t enough, preparation and partnership now define true resilience.
Inside an Email Breach: The 16-Step Response Plan We Use at Fifosys
Over the past few months, we’ve seen a sharp rise in targeted email breaches across UK businesses - including our own clients. When an inbox is compromised, every second counts. This article walks through the exact 16-step plan we follow internally at Fifosys, and includes a download you can adapt for your own response process.